This story is about a bug generated by g++ and clang compilers (at least)
The condition_variables is a feature on the standard library of c++ (libstdc++), when its compiled statically a weird asm code is generated.
Any example on the link below will crash if its compiled statically:
https://en.cppreference.com/w/cpp/thread/condition_variable
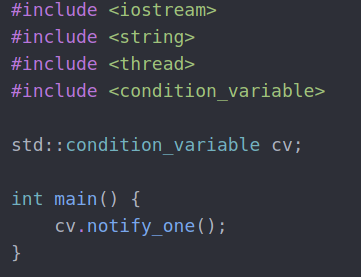
In this case the condition_variable.wait() crashed, but this happens with other methods, a simple way to trigger it:
If this program is compiled dynamically the crash doesn't occur:
Looking the dissasembly there is a surprise created by the compiler:
Compilers:
g++ 9.2.1+20200130-2
clang++ v9
Both compilers are generating the "call 0x00"
If we check this call in a dynamic compiled:
The implementation of condition_variable in github:
https://github.com/gcc-mirror/gcc/blob/b7c9bd36eaacac42631b882dc67a6f0db94de21c/libstdc%2B%2B-v3/include/std/condition_variable
The compilers can't copile well this code in static, and same happens on other condition_variable methods.
I would say the _lock is being assembled improperly in static, is not exacly a null pointer derreference but the effects are the same, executing code at address 0x00 which on linux is a crash on most of cases.







No comments:
Post a Comment